The National Cyber Security Centre Finland’s weekly review – 10/2024
Have you also received a text message that tries to scare you with the consequences of traffic violations? A lot of them have been popping up recently. There are also scams using the name of the suomi.fi service.
I denna veckas översikt behandlas följande
- Text messages threaten people with fines
- Scammers pretend to be various authorities
- Unsecure network edge devices cause a significant risk
- Vulnerabilities
- About the weekly review

Text messages threaten people with fines
During the past week, a large number of reports have been received again on text messages that threaten the recipients with various traffic violations and fines. The messages contain claims such as “Your car was detected driving too aggressively,” or “Your vehicle has been used in certain violations.” The text messages come from Finnish mobile phone numbers, and they contain a link leading to an authentication page phishing for online bank credentials.
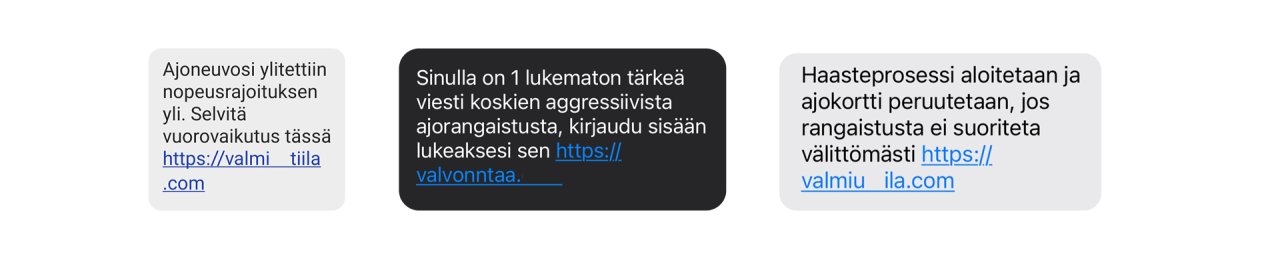
Threatening text messages try to make people click a link to a phishing site.
The messages are a scam. The police do not impose fines or traffic penalty fees via text messages or email. Any traffic penalty fees imposed by the police are sent to the suomi.fi service or by post to the person’s home address.
The link in the scam message does not even try to look like a credible official site; instead, the URL of the link is a word that looks more or less like a Finnish word, such as "yksityiiskohtiin.com". You should not click the link, even though simply clicking it is not yet known to cause any harm. In any case, do not enter your online bank credentials on the scam website behind the link that looks like an authentication page. If you suspect that you have entered your bank credentials on a scam website, you should contact your bank immediately. After that, you can also file a police report.
Scammers pretend to be various authorities
The Digital and Population Data Services Agency has also warned people about new scam messages using the name of the suomi.fi service. The scammer has written the message under the name of the suomi.fi customer service, the customer service of the State of Finland or Finland (“Suomi”). There are several different scam messages going around, both in the form of text messages as well as email. Some text messages ask you to update your information in MyKanta, others pretend to come from the Ministry of Justice or the TE Office.
All of these scam messages have the same purpose: to make victims click the link in the message, thinking that the website behind the link phishing for online bank credentials is a genuine authentication page. However, the authentication page is a fake, and any online bank credentials entered there will end up in the hands of criminals.
Unsecure network edge devices cause a significant risk
Incomplete vulnerability fixes, constant emergency patches, unreliable repair tools and updates that do not work have caused additional risks to organisations that use unsecure devices.
This year, the software vulnerabilities of the network device manufacturer Ivanti in particular have sparked much discussion in the field of cyber security. The authorities of the United States and the United Kingdom have released a stern statement on the topic. A total of five vulnerabilities have been published concerning Ivanti’s Connect Secure and Policy Secure products, three of which have been actively exploited in cyber attacks by state actors. The National Cyber Security Centre Finland (NCSC-FI) has contacted hundreds of parties with online devices regarding Ivanti’s vulnerabilities.
Vulnerabilities
CVE: CVE-2024-27198, CVE-2023-27199
CVSS: 9.8
What: Critical vulnerabilities make it possible to bypass authentication
Product: JetBrains TeamCity software
Fix: Patch
About the weekly review
This is the weekly review of the National Cyber Security Centre Finland (NCSC-FI) (reporting period 1–7 March 2024). The purpose of the weekly review is to share information about current cyber phenomena. The weekly review is intended for a wide audience, from cyber security specialists to regular citizens.